On Tuesday, the U.S. Senate Select Committee on Intelligence convened an open hearing to examine the SolarWinds hack.
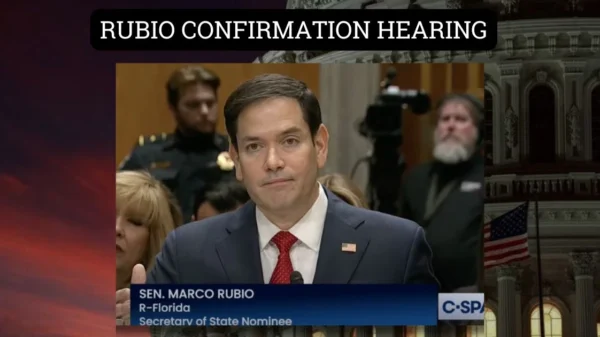
The vice chairman of the committee, U.S. Sen. Marco Rubio, R-Fla., said the following in his opening statement on the hearing:
Thank you Mr. Chairman, for convening this hearing.
I’d also like to welcome our witnesses from Microsoft, Fire Eye, SolarWinds, and Crowd Strike who are here to help the Committee’s examination of the largest cyber supply chain operation ever detected.
We appreciate you being with us this afternoon.
I would note that we also extended an invitation to Amazon to participate and they chose not to.
The operation we will be discussing today utilized Amazon’s infrastructure, at least in part, to be successful. I had hoped Amazon would provide their cooperation.
This cyber operation involved the modification of the SolarWinds Orion platform – a widely used software product– to include a malicious backdoor that was downloaded by up to 18,000 SolarWinds customers between March and June 2020.
Perhaps most insidious about the operation was that it hijacked the very security advice promulgated by computer security professionals to verify and apply patches as they are issued.
There are many concerning aspects to this operation that raise significant questions.
One, my understanding is that if FireEye had not investigated an anomalous event within their own network in November 2020, it is quite possible that this operation would be continuing, unfettered today.
Despite the investment that we have made in cybersecurity, collectively between the government and the private sector, no one detected this activity earlier – and this actor was within SolarWinds network since at least September 2019.
Put simply, how did we miss this? What are we still missing? And what do we need to do to make sure we don’t miss it again?
Second, what exactly did these actors do? Based on what we know – to include what government has stated publicly – the actor seems to have undertaken follow-on operations against a very small subset of the 18,000 networks to which they potentially had access.
Aside from the mechanical aspects of removing a hacker from a network, what do we know about why these actors chose the targets they did, what actions they undertook within those victim networks, and what do we know that we do not know?
And perhaps most importantly, who has the single, comprehensive view of the totality of activity undertaken by this actor?
Third, what is it going to take to rebuild and have confidence in our networks? In speaking with several of you, one of the hallmarks of this operation was the great care taken by the adversary to use bespoke infrastructure and tradecraft for each victim.
Unlike other malware or ransomware clean-up operations, there is no template here that can be used for remediation. What is it going to take to have confidence in both government and private sector networks again?
Fourth, what do we need to do to raise the bar for the cybersecurity of this nation? Is cyber deterrence an achievable goal? How do we need to enhance cybersecurity information logging and sharing across the spectrum to protect against APTs in the future?
And finally, though this is a question for the government, rather than the witnesses here today – what does the United States need to do to respond to this operation?
Government officials initially stated that this was an intelligence gathering operation. Just recently, however, the White House stated, “when there is a compromise of this scope and scale, both across government and across the U.S. technology sector to lead to follow-on intrusions, it is more than a single incident of espionage; it’s fundamentally of concern for the ability for this to become disruptive.”
While I share the concern that an operation of this scale with a disruptive intent could have caused mass chaos, those are not the facts that are in front of us.
Everything we have seen thus far indicates that this was an intelligence operation – a rather successful one – that was ultimately disrupted.
While there are myriad ways for sovereign states to respond, I caution against using terms like “attack” and “act of war” in relation to this operation, unless the facts lead us there. The Chairman knows I always advocate for standing up to our adversaries, but I want to know today what the actor’s intent seemed to be and the extent of the damage.
This Committee, and the rest of the Congress, should consider what policies we need to pursue to better defend our critical networks.
In order to get a fuller view of the problem perhaps we should consider mandating certain types of reporting as it relates to cyber-attacks.
We must improve the information sharing between the federal government and private sector. I look forward to being an active and constructive participant in these debates.
With that, we welcome you and thank you for your testimony and the insights you will share with us and the American people today. It is important that the public understand the current, persistent information conflict the United States finds itself in against nation state adversaries like Russia, China, Iran, and North Korea.
Thank you, Mr. Chairman.